 |
|
|
KACE KBOX 1000 Series (v3.1) by Bob Kelly |
You may have seen
my recent review of the KBOX 2000 series which
(among other things) serves the role of desktop provisioning through unattended
installations and binary image deployments. This is the newer of the two KBOX
appliances available, and I had reviewed the original
KBOX 1000 series back in July of 2005. KACE released a significant update in
v2.0 and so the review was updated in December of
2005. Since that time the 1000 series has continued to grow its feature set and
evolve into what is currently available today: v3.1 of the KBOX 1000 series, and
this will be the focus here.
A quick rundown of what the KBOX 1000 series offers:
-
Software and Hardware Inventory
-
Software Usage Metering (Passive)
-
Software Package Distribution
-
File Synchronization and Replication
-
Self-service User Portal
-
Help Desk and Knowledge Base
-
Reports, Dashboards and Alerts
-
Remote Control Integration
Now much of this was covered back
in the previous reviews, so I will focus my attention on those newer features as
highlighted with hyperlinks to those topics in the list above. I'll finally
close with some quick descriptions of the many features I cannot delve into with much detail in this
review.
While KACE shipped the previous two units to me for testing, I opted to take
them up on a remote access KBOX for this review. Comfortable with the
installation and setup which I have documented in each of the previous reviews,
their test systems are commonly used to demonstrate the abilities of their
appliances for interactive conference calls that they offer potential customers.
Once a customer, they provide 8 to 12 hours of hand-holding referred to as their JumpStart Program. A very helpful
and sharp group of people, this personal attention they provide customers should
be earning them a very good reputation. In fact, IçŸÄ½ told that they record the
JumpStart Program sessions where they walk you through operation of the
appliance and its
configuration for your unique environment and then provide it to you for future reference.
Home > Reviews > KBOX 1000 Series
 |
|
|
KACE KBOX 1000 Series (v3.1) by Bob Kelly |
Documentation is built-in to KACE in more than one location.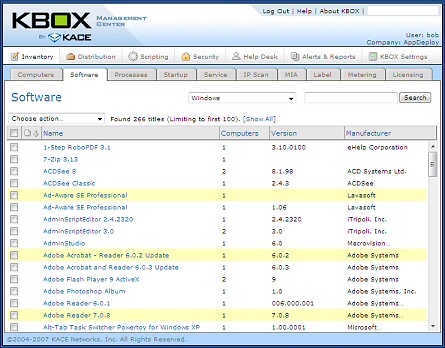 There is a link
at the top for help which opens a PDF Admin Guide of nearly 250 pages. The
documentation is thorough and well organized (even some documentation of the
database structure it uses is provided). Further, on many pages you will find
the most pertinent help displayed on the right margin of the screen. As KACE has
continued to add to the functionality of its product, it is remarkable that the
interface remains uncluttered. Everything is logically laid out to where you
will find what you are looking for in very few clicks even if you don’t know the
lay of the land. If you don’t see what you are looking for, a quick search of the provided
documentation will help you find your way. There is a search field at the top of
the display, but this is for finding collected information (records in your database) and does not
include searches of the documentation.
There is a link
at the top for help which opens a PDF Admin Guide of nearly 250 pages. The
documentation is thorough and well organized (even some documentation of the
database structure it uses is provided). Further, on many pages you will find
the most pertinent help displayed on the right margin of the screen. As KACE has
continued to add to the functionality of its product, it is remarkable that the
interface remains uncluttered. Everything is logically laid out to where you
will find what you are looking for in very few clicks even if you don’t know the
lay of the land. If you don’t see what you are looking for, a quick search of the provided
documentation will help you find your way. There is a search field at the top of
the display, but this is for finding collected information (records in your database) and does not
include searches of the documentation.
Upgrades to the KBOX itself are provided direct from KACE to systems as part of
its maintenance agreement. In fact, I started with v3.1.6596 and was informed
on the home page of the console that v3.1.6748 was available during my review. Like everything else, links to
what you need are right where you would want them to be-- in this case I clicked
on the notice and was then able to
push an “Upgrade Now” button which had a link to release notes right beside it. I for one like to know why I’m upgrading so this a much appreciated
touch.
One of the few things worth restating in this review is the concept of labels
within the KBOX. You can apply labels to almost anything within the KBOX and
then assign scripts, software deployment and other actions to those labels. This
makes it very easy to generate an ad-hoc lists for you to target. On the
computers, software, services, and processes tabs let you select items from the
list and then apply any labels. Additionally you can dynamically apply filters
based on configurable filters.
It can use local (default) authentication or you may label machines based on an LDAP provider like Active Directory. LDAP integration is provided for batch imports of computers and users, and as a live connector for security features like group membership.
Remote Client Provisioning
The client installation can be run interactively, or from the command line
by passing the server name as an argument. It also offers an ID generation
mode so you may include the KBOX client in your baseline image without
duplicating its unique client identifier. When I last looked at the KBOX 1000, one of
the things I really had a problem with was its lack of integrated client
deployment. Today, the KBOX 1000 offers some very good support for remote
deployment. From within the console you can provide a range of IP addresses and
the provisioning agent will attempt to connect and install the agent with the
settings you specify. Like most every task, you can do this once or provide a
number of scheduling options-- this way you can "set it and forget it" with the
KBOX identifying and installing client agents as systems appear on your network.
You can view the results of these installation attempts in the console, which provides enough detail to know just what what went wrong if an attempt should fail. A couple of remote client installation configuration issues to watch for: "Simple File Sharing" must be turned off for Windows XP systems (it requires standard file sharing-- simple file sharing does not support administrative file shares and associated access security). Also if Windows Firewall is turned ON, "File and Print Sharing" must be enabled in the Exceptions list of the Firewall Configuration.
You can also enable file sharing on the KBOX and access the client installation setup files directly in order to script your own client deployment from \\kbox\client\agent_provisioning\. This share on the KBOX is off by default, and must be turned on for remote client provisioning. It is also key to point out that there is now support for more than just Windows clients: Mac, Red Hat Linux and Solaris support is provided for features like distribution, inventory and alerts, but not for all features (in particular these other operating systems do not support scripting and security features today).
Home > Reviews > KBOX 1000 Series
 |
|
|
KACE KBOX 1000 Series (v3.1) by Bob Kelly |
Vulnerability Assessment and Enforcement
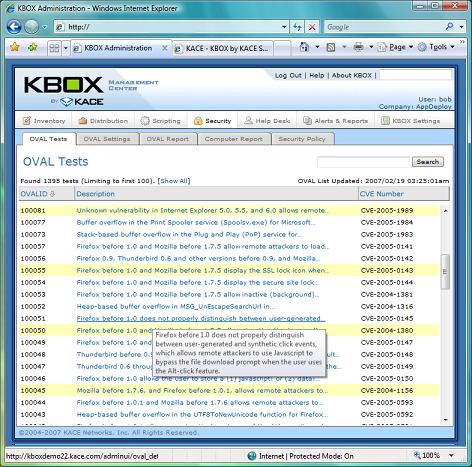 Among
the security features of KBOX, it provides the ability to report on OVAL
vulnerability checks. OVAL is an international standard by the information security community
which serves to promote open and publicly available security content, and to
standardize the transfer of this information across various security tools and services. Generated by Mitre,
its database currently provides over 10,000 tests which may be executed and
reported upon by the KBOX.
Among
the security features of KBOX, it provides the ability to report on OVAL
vulnerability checks. OVAL is an international standard by the information security community
which serves to promote open and publicly available security content, and to
standardize the transfer of this information across various security tools and services. Generated by Mitre,
its database currently provides over 10,000 tests which may be executed and
reported upon by the KBOX.
OVAL relies on definitions submitted by members of the security community, or by the OVAL Board, to detect vulnerabilities. The KBOX allows you to execute these test and view simple reports calling out which systems are deemed vulnerable for each. It is up to you to rectify any vulnerabilities that are uncovered, but armed with the details provided, most all solutions are very straight forward such as implementing specified hotfixes or updating any identified software to a newer version.
KBOX also offers the ability to create and enforce Security Policies, with several "out of the box" policies including:
- Enforce Internet Explorer Settings - allows you to control users' Internet Explorer preferences
- Enforce XP SP2 Firewall Settings - allows you to override, disable or use the user's configuration for Windows Firewall settings
- Enforce Disallowed Programs Settings - allows you to quickly create scripts which disallow the running of certain executables
- Enforce McAfee AntiVirus Settings - allows you to configure what McAfee VirusScan features are installed (for use with McAfee VirusScan version 8.0i)
- McAfee SuperDAT Updater - allows you to build a script to apply McAfee SuperDAT or XDAT updates
- Enforce Symantec AntiVirus Settings - allows you to configure what Symantec AntiVirus features are installed
- Quarantine Policy - disables all network traffic from the target machine-- it permits access to a specified KBOX Server only in order for the below action to allow the machine to be un-quarantined
- Lift Quarantine Action - if you have a machine that has been quarantined from the network using the above Quarantine policy this may be used to turn off the quarantine
Note: these are made up of wizards that build
command line scripts to be deployed and/or scripts that set policy keys in the
Windows registry.
Patch Management
The
patch management support offered by the KBOX provides a workflow to help identify which new bulletins have not been
viewed. You may review and acknowledge them by setting an approval status. The
rules for patch
settings let you handle how they are managed when they arrive.
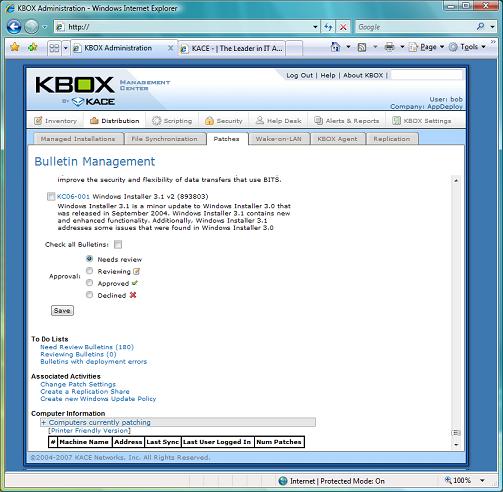
This provides a nice way to say on top of updates using a simple workflow. All patches are provided by year, criticality or approval status. When viewing the details of a patch, the systems affected are listed at the bottom of the page. From the Distribution > Patches tab you can perform any of the following actions:
- Filter and search patch bulletins
- Approve or decline bulletins
- Configure and troubleshoot patch deployment
- Create a new Replication Share
- Create a new Windows update policy
- See a list of computers currently patching
- Run patch reports
- Click to expand list of bulletins that require attention
- Click to view bulletins by year, severity, or status
- View patch status.
The KBOX downloads all patches to the KBOX nightly where they are flagged with a “Needs Review” status unless automatic patching has been turned on. With automatic patching on, the patches are automatically deployed to the specified groups (such as a group of test systems). The KBOX determines which patches are appropriate for each individual system and distributes accordingly.
Home > Reviews > KBOX 1000 Series
 |
|
|
KACE KBOX 1000 Series (v3.1) by Bob Kelly |
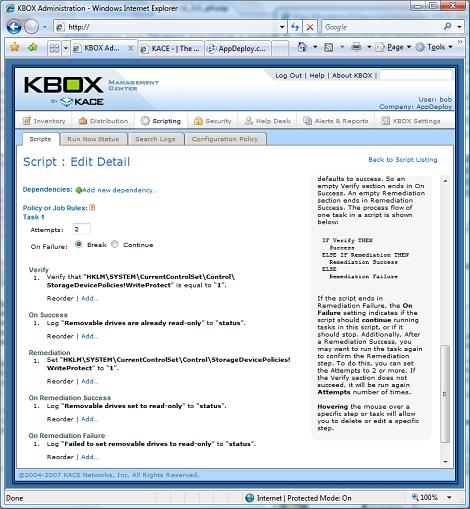 To say scripting is a feature is a bit vague, does this mean you can run scripts
on remote systems the way you would deploy a command line installation? Well,
yes and no—the scripting support of the KBOX goes quite a bit further.
Specifically, it provides a way to conditionally run commands and affect changes
to a machine without writing a script at all. At least not a traditional
script.
To say scripting is a feature is a bit vague, does this mean you can run scripts
on remote systems the way you would deploy a command line installation? Well,
yes and no—the scripting support of the KBOX goes quite a bit further.
Specifically, it provides a way to conditionally run commands and affect changes
to a machine without writing a script at all. At least not a traditional
script.
Tasks are the individual steps being carried out by the script. In each script,
you can have any number of tasks. Whether or not a task is executed is dependent
upon the success or failure of the previous task and any rules for performing
subsequent tasks.
There are two types of scripts you can create: policies and jobs. Policies are
generally used to perform tasks that will be repeated, such as checking to see
whether McAfee Antivirus is installed and working. Whereas jobs are used to perform
one-time tasks, such as uninstalling software or moving files. You may specify criteria to determine who runs the script and on what schedule
it should be run.
A scripting job can contain several steps broken up into the following
functional elements:
- Verify – your “If” statement, what you want to check for (if anything)
- On Success – If the item you have verified is true, this action is to be taken
- Remediation – If the "verify" check does not resolve true, this action is taken
- On Remediation Success – If the remediation action is successful, this action is taken
- On Remediation Failure – If the remediation action is not successful, this action is taken
So for those keen on scripting, the VBScript
equivalent of this logic would appear as follows:
If <Verify> then
<On Success>
Else
<Remediation>
If Error then
<On Remediation Failure>
Else
<On Remediation Success>
End If
End If
There are quite a few built in actions you can choose for each element.
Some
examples include: search the file system, verify a file or directory, verify the
status of a process or service, and check for registry keys and values. You can
even check the number of subkeys at a certain level of the registry.
Essentially, they have done a very good job of providing built in steps which
will cover most checks and actions you might want to use. When you choose one of
these provided steps, you are then prompted to
enter its parameters. For example, if you said you wanted to verify a service
was running, you would need to specify the service name.
In the very few areas where I find room for improvement, it would be nice to see
an option to select from a list of known values for these parameters. In the
example of checking for a process, KBOX knows all the processes that have been
detected on your network, so it would be helpful it this knowledge was used to provide a list
(to help ensure you don’t mistype
such a value-- some process names include a file extension and some do not). The
selection options might be provided for services, software and other collected data.
With the power behind this features, I can easily find those getting used to
this interface desiring this control for software deployment (as opposed to the
simpler built-in distribution
support). Instead of installing and reporting success or failure, this would
allow you the ability to verify dependencies, what actions are
taken, what is logged, what is done in the event of a failure, etc.
Home > Reviews > KBOX 1000 Series
 |
|
|
KACE KBOX 1000 Series (v3.1) by Bob Kelly |
More stuff (in brief)
Far too much to cover in these few pages, I recommend seeing for yourself. But
rather than just leaving it at that, here are a handful of other cool things I
wanted to point out:
- There is a fairly robust help desk feature which supports the opening of tickets via email or (as you'd expect) using a web form on the KBOX. It's fields are customizable and it offers escalation rules making it more than a rudimentary helpdesk implementation.
- A knowledge base system is also provided for publishing info to help users to help themselves. You can also limit access to articles so that you can show some to users and some only to administrators.
- There is an MSI wizard provided to help you create MSI deployment jobs (though the wizard does not filtering for only MSI files, so you'll need to know which are Windows Installer setups and which are not).
- Remote Control integration – at this point, remote control is not provided a service of the client. Instead, the KBOX provides integration points so that you may deploy your remote control solution of choice and easily trigger it at key locations within the KBOX management console. UltraVNC is bundeled with the KBOX and to make things even easier, one of the wizards provided under Scripting > Configuration Policy is a UltraVNC Wizard. This wizard helps you easily deploy this popular freeware remote control utility.
- There is no bandwidth throttling, but you can specify a threshold for how many clients may connect to the KBOX at a time. BITS is supported for client downloads (off by default, but can be turned on in XML settings file at client)
Worthy of more than a simple bullet here is support for multiple sites. As a system intended for small to mid-sized networks, I was not very surprised when I was told there was no inherent support for implementing more than one KBOX and having them communicate via WAN links. However, I was surprised to hear that there was considerable thought (and a cost effective solution implemented) in place of a multi-server configuration: Sites may be defined (again with labels) and you may optionally provide a alternate share location for accessing the binaries that would normally be associated with software or patch distributions and script dependencies. This way, you can have one KBOX and any remote sites communicating over WAN links, could look locally to access the payload for high-bandwidth tasks such as software deployment. Further, KBOX provides support for "Replication Shares" which allow a KBOX Client to replicate to a share for this purpose.
Closing
The KBOX is a very impressive solution and offers a great deal of functionality in a intuitive management console. It clearly goes a long way to helping small to mid-sized environments with a minimal, moderately technical staff, enjoy the management benefits that are more commonly associated with large enterprise environments that have a staff of senior engineers. Just managing similar systems can be a full time job, and from there the value that is enjoyed from having it is heavily dependant upon the talent of the administrators who work with it. Here, the KBOX does well to reduce the complexity of scripting, software deployment and remote client management. While I’m sure that it will be a selling point for may, I've not even discussed the fact that this it is actually an appliance solution: just plug the server in (with no real installation necessary) and no new server need be set aside to handle its load. Even with this strong benefit intentionally omitted from this review, KBOX is clearly a serious contender for your management solution due to what it does (more than what it is).
Bob Kelly
AppDeploySM
2/24/2007

Comments