None of us love all applications equally. For one, there are those applications our users just aren't supposed to be running: Streaming video. Elf bowling. Unapproved instant messaging. Try as you might, you'll never stop your users from getting to all of them. These things kill productivity, hammer the network, and half the time seem packed with junkware, spyware, and who knows what else. And those are just the applications your users know they're not supposed to be running. There's also that whole class of "quasi-business" applications that have an arguable business benefit – but which your company hasn't paid for, isn't licensed to use, and doesn't want. Those can not only cause support issues, but outright financial damage if you're caught. How can you stop them all?
It's tough. Windows' primary function, after all, is to run applications, and it does a pretty good job at it. Getting it to not run applications kind of goes against the grain. In Windows XP and Windows Server 2003, Microsoft introduced a new technology called Software Restriction Policies (SRP), a part of Group Policy that was intended to keep unwanted applications from running. Essentially, you'd make a big list of all the applications you wanted to permit, and nothing else could execute. The technology more or less flopped. Oh, organizations definitely use it, and it works exactly as advertised, but the process of assembling and maintaining that list of approved applications can be incredibly complicated and time-consuming. Many, many organizations simply don't have the time or resources, and so they gave SRP a miss.
That was 12 years ago. Hasn't anything better come along?
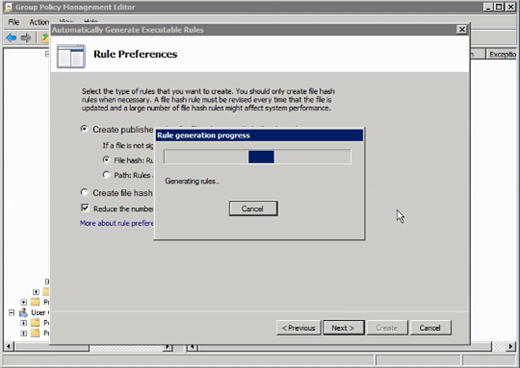
Now the Group Policy Editor includes Applocker, and in this video I explain how to create an app whitelist using Applocker.

Comments