How to get KACE to run a batch file that calls upon a windows command script to run
I am to block IE 11 from being downloaded as many of our applications only work with IE9. MS has a command script it has published to do this. It needs to run with an elevated CMD. I have created a batch file that calls upon the MS command script and adds the registry file that blocks IE 11 and it works within itself. Now I need to figure out a way to push that Batch file down to the rest of the users. Bellow is my batch file followed by the MS command script. Any help would be awesome.
My Batch file:
@echo off cd "C:\ProgramData\Dell\KACE\kbots_cache\packages\kbots\111" ---(where the IE11_blocker.cmd file can be found) ie11_blocker.cmd /b
The MS command script:
@echo off Echo MICROSOFT TOOL KIT TO DISABLE DELIVERY OF
Echo INTERNET EXPLORER 11
Echo.
Echo Copyright (C) Microsoft Corporation. All rights reserved.
Echo. set ProductName=Internet Explorer 11
set REGBlockKey=HKLM\SOFTWARE\Microsoft\Internet Explorer\Setup\11.0
set REGBlockValue=DoNotAllowIE11 set RemoteMachine=%1 if ""=="%1" goto Usage
if "/?"=="%1" goto Usage
if /I "/H"=="%1" goto Usage
if /I "/B"=="%1" goto LocalMachine
if /I "/U"=="%1" goto LocalMachine
set RemoteMachineName=%1
set Action=%2 :Parse
if /I "/B" == "%Action%" goto Block
if /I "/U" == "%Action%" goto UnBlock
goto Usage :Block
Echo Blocking deployment of %ProductName% on %RemoteMachineName%
REG ADD "\\%RemoteMachine%\%REGBlockKey%" /v %REGBlockValue% /t REG_DWORD /d 1 /f
goto End :UnBlock
Echo Unblocking deployment of %ProductName% on %RemoteMachineName%
REG DELETE "\\%RemoteMachine%\%REGBlockKey%" /v %REGBlockValue% /f
goto End :LocalMachine
echo LOCAL!
set Action=%1
set RemoteMachine=.
set RemoteMachineName=the local machine
goto Parse :Usage
Echo.
Echo This tool can be used to remotely block or unblock the delivery of
Echo %ProductName% via Automatic Updates.
Echo.
Echo ------------------------------------------------------------
Echo Usage:
Echo %0 [machine name] [/B] [/U] [/H]
REM [machine name] [/B|U|H]
Echo B = Block %ProductName% deployment
Echo U = Allow %ProductName% deployment
Echo H = Help
Echo.
Echo To block or unblock installation on the local machine use
Echo period ("." with no quotes) as the machine name
Echo.
Echo Examples:
Echo %0 mymachine /B (blocks delivery on machine "mymachine")
Echo.
Echo %0 /U (unblocks delivery on the local machine)
Echo ------------------------------------------------------------
Echo. :End
2 Comments
[ + ] Show comments
-
Would it be simpler to just create the registry edit and push that change down? - AFCUjstrick 10 years ago
-
we have that in place now, but for whatever reason even though the the command script adds the same registry key we are doing manually it does not prevent IE11 from being updated through windows update. However once the command script is run it does block the install of IE 11. We have since moved on and are just pushing this from the .adm file and just adding it to our GPO. However just for future knowledge it would be great if anyone has any ideas, on how to get this to push from Kace. - jgolden 10 years ago
Answers (2)
Please log in to answer
Posted by:
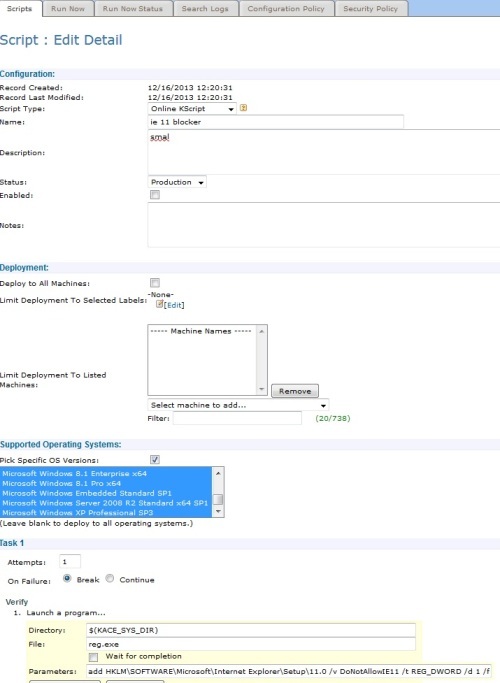
SMal.tmcc
10 years ago
Create a kscript and dump the command file.
Comments:
-
you may also have to push "reg add hlkm64\...." for 64 bit machines if it does not take with the 32 bit reg call - SMal.tmcc 10 years ago
Posted by:
jgolden
10 years ago